AWS Config Rule: Kinesis Firehose Encryption
CHECK_FOR_ENCRYPTION_KINESIS_FIREHOSE
Ryan Ware
Last Update 10 months ago
Description: Checks whether Kinesis Firehose have Encryption Enabled.
Trigger type: Periodic
AWS Region: All supported AWS regions
How to Resolve Manually
To enable server-side encryption (SSE) on your Amazon Kinesis Firehose delivery stream, you must ensure that SSE is enabled on your Kinesis Data Stream if this is to be your source. Enable Data Stream encryption first, before attempting to encrypt the Firehose.
Server-side encryption - Kinesis Data Firehose supports Amazon S3 server-side encryption with AWS Key Management Service (AWS KMS) for encrypting delivered data in Amazon S3. For more information, see Protecting Data Using Server-Side Encryption with AWS KMS–Managed Keys (SSE-KMS).
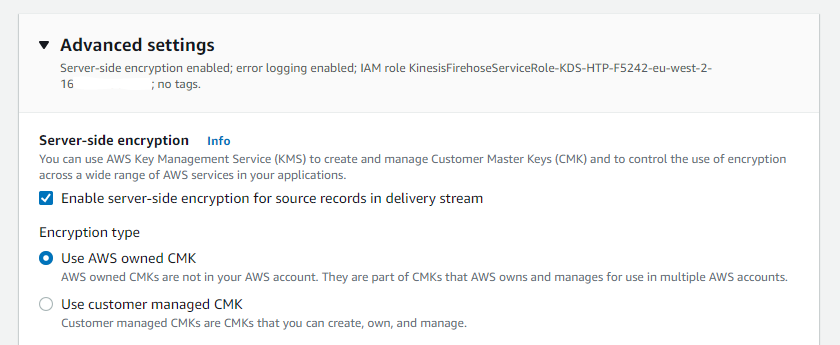
If your Amazon Kinesis Firehose is setup to use Direct PUT as a source, you can enable server-side encryption (SSE) by heading to the Advanced Settings within your Amazon Kinesis Firehose delivery stream configuration.
Here, you can enable the encryption and choose from either using the AWS owned Customer Managed Key (CMK) or using a customer managed CMK from your Key Management Store (KMS) to encrypt the delivery stream.
How to Resolve with StackZone
StackZone will be able to automatically enable encryption on your Amazon Kinesis Firehose Delivery Streams if you enable this remediation. The remediation action will use the AWS managed CMK (aws/kinesis) when performing the encryption of your Amazon Kinesis Firehose Delivery Streams
This will then ensure that your resources are marked as COMPLIANT with the AWS Config Rule.
To enable this within your own StackZone deployment, head on over to Baseline Services > AWS Config Rules Regional > Kinesis Firehose Encryption and enable the remediation.
Want to know more about StackZone and how to make your cloud management simple and secure?
Check our how it works section with easy to follow videos or just create your own StackZone Account here


