AWS Config Rule: CloudTrail Encryption Enabled
CLOUD_TRAIL_ENCRYPTION_ENABLED
Fernando Honig
Last Update 2 ani în urmă
Description: Checks whether AWS CloudTrail is configured to use the server side encryption (SSE) AWS Key Management Service (AWS KMS) customer master key (CMK) encryption. The rule is compliant if the KmsKeyId is defined.
Trigger type: Periodic
AWS Region: All supported AWS regions
How to Resolve Manually
To resolve this manually, you will need to ensure that your CloudTrail trails are encrypted with an AWS KMS Key.
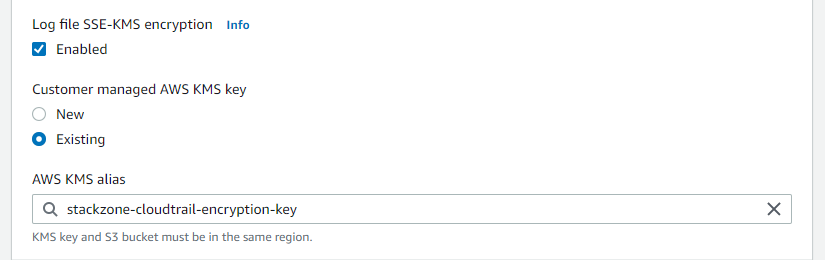
You can configure this easily by editing your trail, and enabling Log file SSE-KMS encryption as pictured below. You will then either need to create a new Customer managed AWS KMS key or choose an existing one that your already have stored.
Want to know more about StackZone and how to make your cloud management simple and secure?
Check our how it works section with easy to follow videos or just create your own StackZone Account here


