AWS Config Rule: RDS Instance Default Admin Check
RDS_INSTANCE_DEFAULT_ADMIN_CHECK
Eduardo Van Cauteren
Last Update há um ano
Description: Checks if an Amazon Relational Database Service (Amazon RDS) database has changed the admin username from its default value. This rule will only run on RDS database instances. The rule is NON_COMPLIANT if the admin username is set to the default value.
Trigger type: Configuration changes
AWS Region: All supported AWS regions except China (Beijing), China (Ningxia) Region
How to Resolve Manually
A general security recommendation is not to use the default admin usernames for resources. This rule checks that 'postgres' or 'admin' usernames are not being used for any of the RDS Instances. If one of those usernames are found in any of the RDS Instances the rule will be marked as non-compliant.
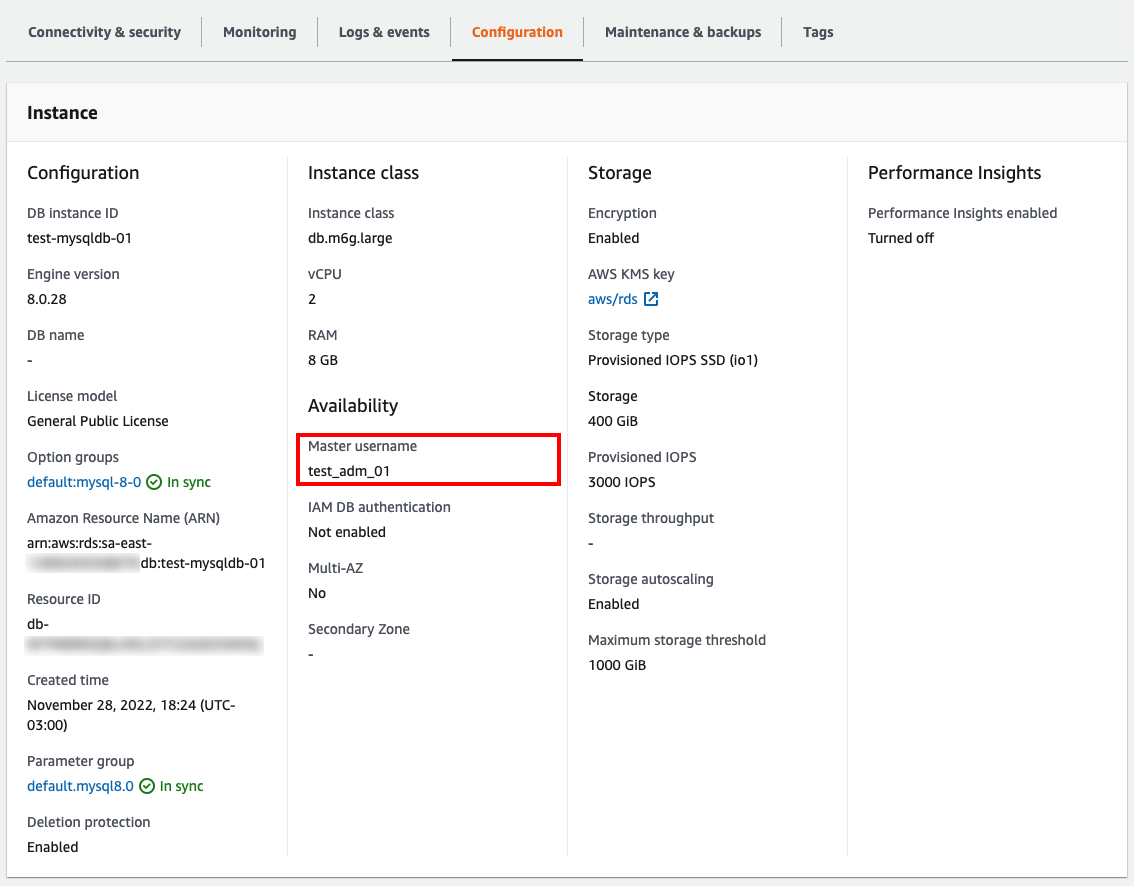
To check the current master username of an instance, head to AWS Console, go to RDS and click on DB Instances from within the Dashboard. Check that any of the listed DB Instances have the master username different than 'postgres' or 'admin'. Use the following screenshot as a reference:
AWS indicates in the documentation that you can't change the master user name after the DB instance is created, so you will have to develop an appropriate process that fits the needs of your current infrastructure.
Want to know more about StackZone and how to make your cloud management simple and secure?
Check our how it works section with easy to follow videos or just create your own StackZone Account here


