AWS Config Rule: VPC Restricted Common Ports Policy
RESTRICTED_INCOMING_TRAFFIC
Ryan Ware
Last Update منذ ٨ أشهر
Description: Checks if the security groups in use do not allow unrestricted incoming TCP traffic to the specified ports. The rule is COMPLIANT when the IP addresses for inbound TCP connections are restricted to the specified ports. This rule applies only to IPv4.
Trigger type: Configuration changes
AWS Region: All supported AWS regions
How to Resolve Manually
"Common Ports" in this scenario would be in relation to the following TCP Ports;
- Port 20 (FTP)
- Port 21 (FTP)
- Port 3389 (Windows RDP)
- Port 3306 (MySQL)
- Port 4333 (mSQL)
If you have an EC2 Security Group created with custom ingress rules, you will need to ensure that any inbound traffic to these five ports are controlled by restricting the ingress rule to a specific IP.
For example, if you allow a rule for Port 20 in your Security Group to 0.0.0.0/0 (all), this will be marked as NON_COMPLIANT. You will need to ensure that this Port 20 rule is restricted by IP, similar to the example shown below which features two rules in a particular Security Group.
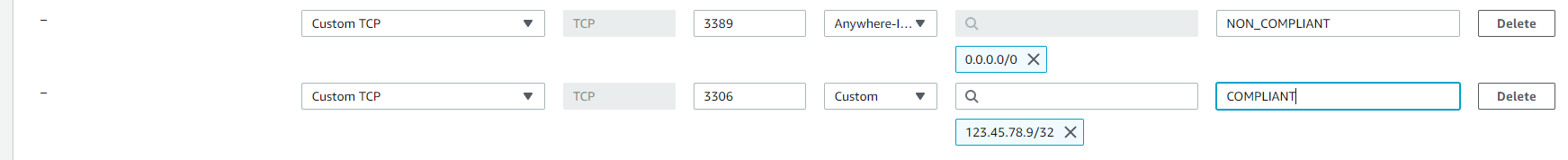
The Rule added for Port 3306 has a Custom Source, locked to a specific IP for inbound access, whereas the Rule for Port 3389 is "open to the world" from an ingress perspective and that is potentially dangerous if the Instance this Security Group is attached to is within a Public Subnet. It means anyone can access this instance on that Port.
Resolving this will take some time, as you will need to audit all NON_COMPLIANT Security Group resources to find which rules are causing your resources to be NON_COMPLIANT. You will then need to lower the scope of your ingress rules to restrict access.
Want to know more about StackZone and how to make your cloud management simple and secure?
Check our how it works section with easy to follow videos or just create your own StackZone Account here


